Cloud Security
Peel Back the Layers of Your Cloud
Our Cloud Penetration Test evaluates your cloud environment against the latest adversary tradecraft to provide valuable and targeted insights into both tactical and strategic measures that yield the greatest defensive impact.
Secure Your Cloud
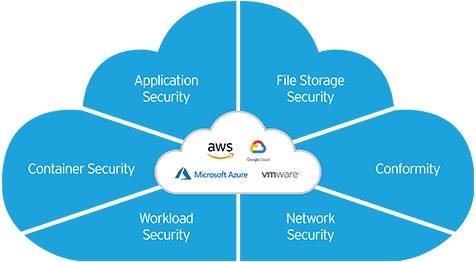
Per Gartner, human error accounts for as much as 95% of cloud breaches. Attackers persistently scan the internet to exploit these security weaknesses. InvokeSec’s cloud penetration testing services are designed to pinpoint configuration problems and vulnerabilities within your Azure, AWS, or Google Cloud Platform (GCP) infrastructure.
We’ll Execute Regardless of the Environment
We tailor testing to suit any cloud environment, system, and target, incorporating the attack scenarios that concern you the most. Whether it’s a breached cloud application or service, a compromised or malicious user, or entirely custom objectives, you have complete power and control in setting the desired outcomes of the engagement. Our team of experts can emulate the realistic approach of a skilled adversary exploiting cloud misconfigurations, compromising systems, escalating privileges, and endangering sensitive data in a true-to-life attack scenario.


Azure Penetration Testing
Microsoft Azure penetration testing is essential for ensuring the security of your cloud infrastructure, whether you’re in the middle of a migration, developing applications, or in the thick of an audit. InvokeSec identifies cloud-specific vulnerabilities present in your Azure environment and internet-exposed applications. The testing doesn’t stop there, as we discover credentials, enumerate excessive privileges, and identify misconfigurations that can lead to the compromise of your Azure infrastructure and allow an attacker to access sensitive data, seize Azure resources, or pivot to attack your internal network.
AWS Penetration Testing
InvokeSec’s AWS penetration testing methodology assists you in detecting cloud security vulnerabilities that can lead to increased risk and exposure. This type of testing is crucial if your organization is rebuilding or expanding cloud infrastructure, developing cloud applications, or performing compliance and audit requirements. Our testing team of experts uncovers weaknesses, exposed credentials, and cloud misconfigurations to gain access to restricted resources, escalate user privileges, and reveal sensitive information. The testing also detects internet-exposed management interfaces, open and accessible S3 buckets, and security gaps in AWS Identity and Access Management (IAM) configurations.

Google Cloud Platform Penetration Testing
For organizations migrating to Google Cloud, developing applications in GCP, or using Google Kubernetes Engine (GKE), Google Cloud penetration testing is an effective way to baseline security. During these tests, InvokeSec goes beyond automated scanning to manually exploit vulnerabilities and misconfigurations, identifying security gaps in your Google Cloud attack surface that adversaries can potentially exploit.
What You Can Expect
See Your Cloud Through the Eye of a Skilled Attacker
Experienced cloud assailants act and attack differently. Our experience provides a genuine representation of the potential outcomes if a proficient adversary targeted your cloud assets.
Customize Testing for Your Most Feared Scenarios
Evaluate protections against your defenses. They’ve cost millions. But do you know how effective they are?
Uncover Weaknesses Overlooked by Automated Tools
Relying solely on misconfigurations and automated scanning is not enough. Discover the complete range of external and internal routes attackers could leverage to access sensitive resources.
Concentrate Time and Resources on High-Impact Areas
Time is invaluable. Focus your team’s remediation efforts on critical issues that attackers are most likely to exploit. Every report comes with real-world risk ratings and remediation recommendations.
Forge a Roadmap to Enhanced Cloud Resilience
Prevent repeating past mistakes. Obtain collective commitment from functional leaders to support long-term initiatives aimed at reinforcing cloud environments against future threats.
Continuous Education
Prevent simulations from becoming reality. The CourseOps platform educates defensive teams, so they stay ahead of the latest attacks. Focus on prescriptive recommendations that remediate the highest risk to your organization.